In the red team, enumeration is one of the important steps. Enumerating subdomains is important for discovering potential weak links or easy-to-attack areas of a web application.
Today, we will learn all about the sublist3r tool.
Sublist3r is one of the best tools to use for looking up subdomains. This is an open-source tool written in the Python programming language.
It gathers information from various sources, such as search engines, passive DNS databases, and social media platforms.
Installing Sublist3r
Sublist3r tool comes pre-packaged in Kali Linux.
We don’t need to go to a GitHub repository to install the tool and the packages required to run it.
To install sublist3r through the Kali Linux repository.
sudo apt-get install sublist3r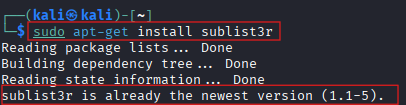
As you see above image, it looks like the tool is already installed in the system.
Detailed Options
| Flag | Description |
|---|---|
| -d | To enumerate subdomains from the specific domain. |
| -b | To discover subdomains by brute-forcing possible or common names. |
| -p | Discover subdomain by matching specific open ports |
| -v | To view results in real-time as they discovered. |
| -t | Set the number of threads used during brute-forcing mode. |
| -e | To scan subdomain through certain search engines. |
| -o | To save results to a specific text file. |
| -h | To view available options and get a quick reference. |
Usage
- Help page
sublist3r -h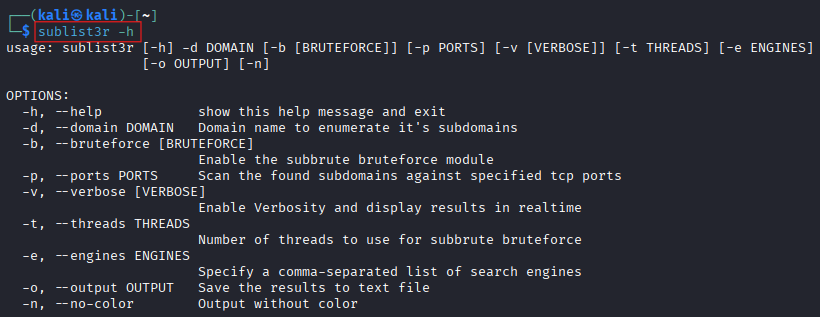
From this help page, you can get all the information about all the options that can be used by this option.
- Enumerate subdomains of a specific domain.
sublist3r -d cyberthreatinsider.com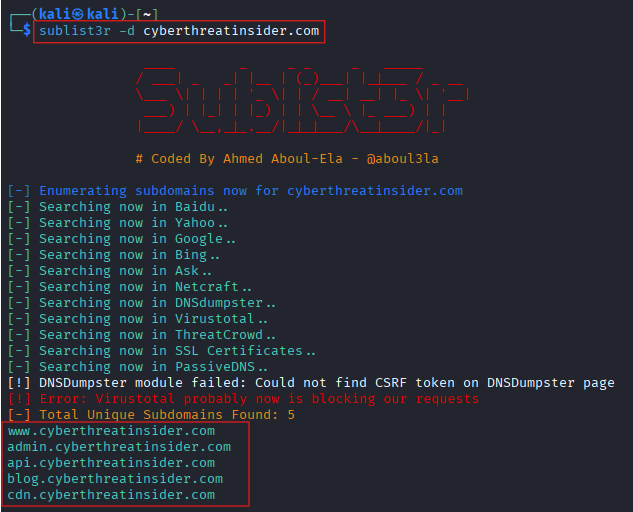
Use this if you want to just find a subdomain of a specific domain.
- Enumerate subdomains which have open ports.
sublist3r -d cyberthreatinsider.com -p 22,80,443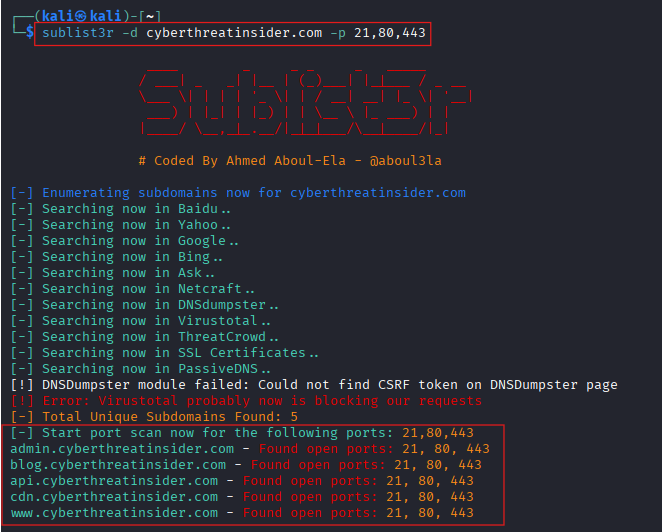
By this option, some subdomains will be eliminated if they don’t have the same open ports as mentioned in the command.
- View the result in the Realtime.
sublist3r -d cyberthreatinsider.com -v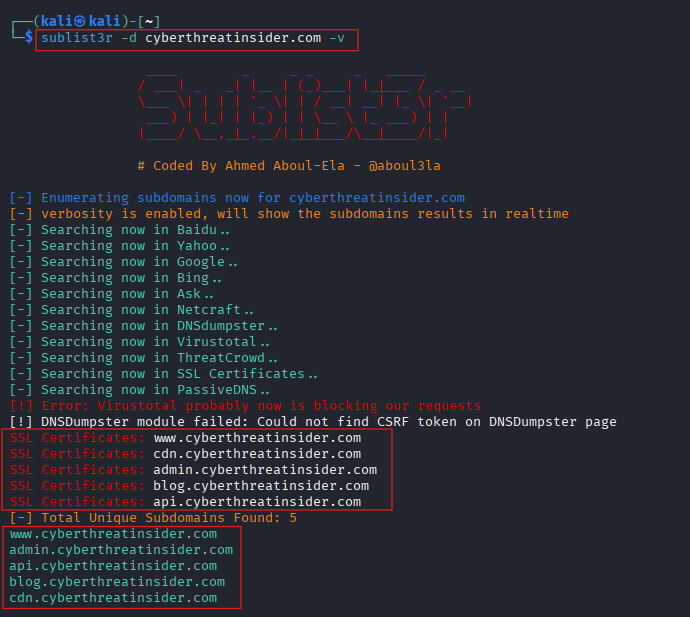
- Brute forcing attack
sublist3r -d cyberthreatinsider.com -bSublist3r tool uses Subbrute as a module to brute-force subdomains.
- Use specific search engines.
sublist3r -d cyberthreatinsider.com -e ssl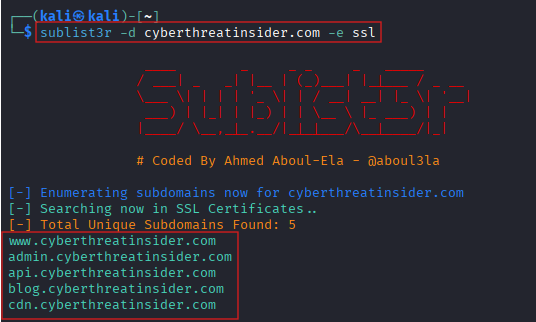
Conclusion
Enumerating subdomains gives valuable insights about the target. It helps to automate the process and effectively discover juicy links.
By following the article, you may get a small picture of what really a sublist3r is. Comment below if you are facing any issues or have any questions.


