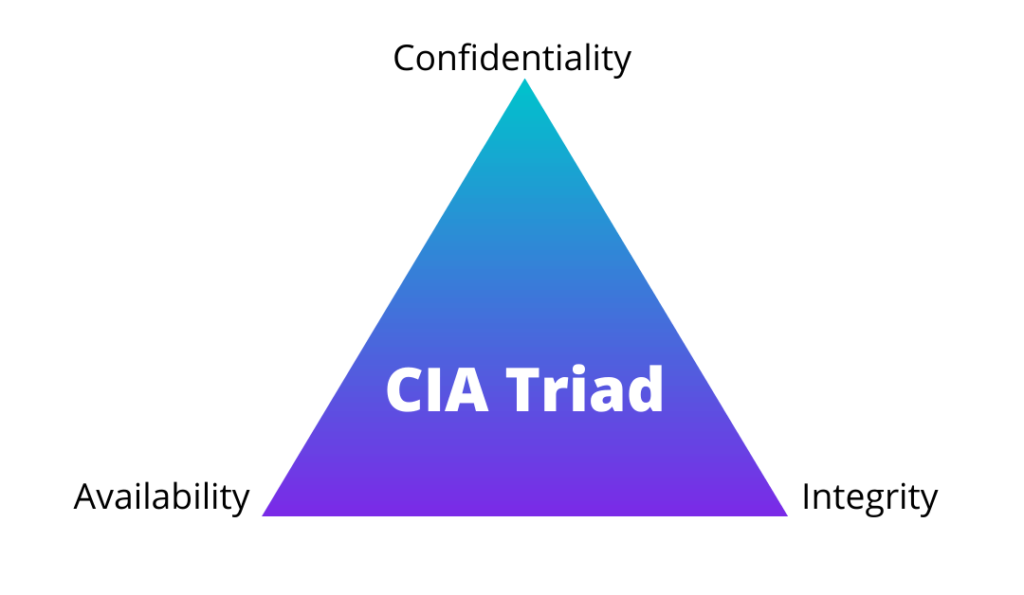
CIA Triad
The CIA Triangle or CIA Triad is one of the most prominent models for guiding information security policy in any organization. CIA is the most basic model used in Network Security.
They should serve as goals and objectives for all security programs. The CIA triad is so fundamental to information security.
When data is exposed, you can be sure that one or more of these principles has been broken.
When a cyberattack happens to any organization or a user falls victim to phishing, you can be sure that one or more of these principles has been violated.
The CIA Triad is a model for guiding information security policy within organizations. It was developed by the Central Intelligence Agency (CIA) as part of its Information Security Policy Framework in the 1970s. This framework provides guidance for developing policies and procedures to protect classified information.
Why is the CIA Triad essential?
We may ask specific questions as we plan and spend money: Does this tool make our information more secure? Does this service help to secure the integrity of our data? Will improving our infrastructure make our data more accessible to those who require it?
It’s helpful to think of the CIA triad as a method to make sense of the overwhelming number of security software, services, and approaches on the market. Instead of just throwing money and experts at the nebulous “issue” of “cybersecurity.”
Furthermore, grouping these three concepts into a triad emphasizes that they frequently exist in conflict . We’ll look at some specific examples later.
Extensive authentication for data access may help to keep it secret. Still, it may also make it hard for individuals with the right to review that data to do so, limiting availability.
While designing an information security strategy, the organization makes practical decisions about all three components.
The three pillars of the CIA Triad
CIA stands for
- Confidentiality
- Integrity
- Availability
These are the goals that should be kept in mind when protecting a network.
Confidentiality
Confidentiality refers to the ability of only authorized individuals/systems to read confidential and sensitive information. Unauthorized persons should not have access to the data transmitted across the network. The attacker may attempt to gather data using various tools accessible on the Internet to access your information. The critical approach to avoid this is implementing encryption techniques to protect your data. Even if the attacker has access to it, they will be unable to decipher it. AES (Advanced Encryption Standard) and DES are two encryption technologies (Data Encryption Standard). A VPN tunnel is another technique to safeguard your data.
Confidentiality can be breached in various ways, including direct attacks ability to attain unauthorized access to systems, applications, and databases to steal or tamper with data. Examples include network reconnaissance and various sorts of scanning, electronic eavesdropping (through a man-in-the-middle attack), and an attacker escalating system privileges. However, confidentiality can be breached accidentally due to human mistakes, negligence, or insufficient security procedures.
Countermeasures to protect confidentiality include:
- Data classification and labeling
- Full access restrictions and authentication procedures
- Data encryption in process, transport, and storage
- Steganography
- Remote wipe capabilities
- Proper education and training for all personnel with data access
Integrity
The goal of integrity is to ensure that data is immutable. Data corruption is a failure to maintain data integrity. We utilize a hash function to determine whether or not our information is updating.
SHA (Secure Hash Algorithm) and MD5 (Message Direct 5) are the encryption methods used to ensure integrity.
If we use SHA-1, MD5 is a 128-bit hash, while SHA is a 160-bit hash. Other SHA techniques that we may utilize are SHA-0, SHA-2, and SHA-3.
An attacker can compromise integrity intentionally through an attack vector.
Integrity compromised through:
- Tampering with intrusion detection systems
- Modifying configuration files
- Changing system logs to avoid detection
- Unintentionally through human error
- Coding errors
- Inadequate policies, procedures
- Protection mechanisms
Trusted certificate authorities (CAs) issue digital certificates to organizations to verify their identity to website users.
Encryption, hashing, digital signatures, and digital certificates are cryptographic methods to ensure data integrity.
Availability
The network’s availability implies that it should be easily accessible to its users. This scenario is actually for both systems and data. Network administrators should maintain infrastructure, perform regular updates, prepare for fail-over, and avoid bottlenecks to guarantee network availability. DoS or DDoS attacks may cause a network to become inaccessible when its resource is consumed. The consequences might be severe for businesses and people that rely on the Internet as a business tool. As a result, sufficient precautions should be avoided such attacks.
Many factors might risk availability, including hardware or software failure, power failure, natural disasters, and human mistakes.
The most well-known attack that threatens availability:
- Denial of Service (DOS) attack
- Maliciously degrade any web application like web-based service, website, or live system.
Redundancy, hardware fault tolerance, frequent software patching, system upgrades, backups, thorough disaster recovery plans, and denial-of-service prevention solutions are all suggested to ensure availability.
Implementation of the CIA Triad
It is not enough to understand the CIA Triad; one must also understand the order of the three based on numerous conditions. CIA Triangle will then put it into action properly. Factors might include:
- An organization’s security goals.
- The nature of the business.
- The industry.
- Any applicable regulatory requirements.
Consider the case of a government intelligence service. Without question, the most crucial aspect of such organizations is secrecy. On the other hand, if you must pick a financial institution, honesty is the most vital factor since precise records of transactions and balances can avoid catastrophic losses. Healthcare and e-commerce, on the other hand, must prioritize availability to minimize downtime or loss of life.
It is also vital to remember that emphasizing one or more of the CIA Triangle principles may impact the others. For example, a system that demands necessary privacy and integrity may have to forego the fast performance that other systems want or require. This compromise is not permanently damaging because the judgments are made carefully and with experience. As a result, each company must select how to execute the CIA Triangle depending on their needs.
Conclusion
In this article, you learn the foundation of information security. It is one of the pillars of information security adopted by every organization.


